Cybersecurity remains a hot topic. Even after several decades of “living in the cyberspace”. And feeling safer when browsing and surfing online would be nice. This article about feeling safer with the NIST Cybersecurity Framework, or NIST CSF. It introduces you to what this framework has to offer. And why you should consider benefiting from it too. Whether you pay a visit to the Web while at your office, or while at home.
It is a Framework
The National Institute of Standards and Technology, or NIST, was founded in 1901 and is now part of the U.S. Department of Commerce. The development of the Cybersecurity Framework started in 2013. It is a collaboration between industry and government.
The framework consists of standards, guidelines, and practices to promote the protection of your critical assets. For instance, your confidential information. The approach of the framework helps owners of these assets to manage risks while visiting the cyberspace. NIST CSF is therefore a risk-based approach to protect you from threats and vulnerabilities that you are exposed to.
Given it being a framework, it inherently means that you have the freedom to adopt and adapt those components that you deem of most value to you. It also means that your existing cybersecurity practices that work well, can be “plugged in” easily into the framework. In other words, you build on what you have. Assuming, of course, that the practices that you have in place are effective.
NIST CSF Explained
The NIST cybersecurity framework consists of the following components.
- The Framework Core
- The Implementation Tiers
- The Framework Profile
The Framework Core

The Core is a set of desired cybersecurity activities and outcomes organized into Categories and aligned to Informative References. The Framework Core is designed to be intuitive. As well as to act as a translation layer to enable communication between the different teams of your organization by using simplistic and non-technical language.
The Core consists of three parts:
- Functions
- Categories, and
- Subcategories.
The Core includes five high level functions:
- Identify
- What needs protection?
- Protect
- What safeguards are available to protect you?
- Detect
- What helps me to detect a breach?
- Respond, and
- What can contain the impact of a breach?
- Recover.
- What can help me recovering from a breach?
These 5 functions are not only applicable to cybersecurity risk management, but also to risk management at large. Think of organizational risk management.
The next level down is the 23 Categories. Those are split across the five Functions.
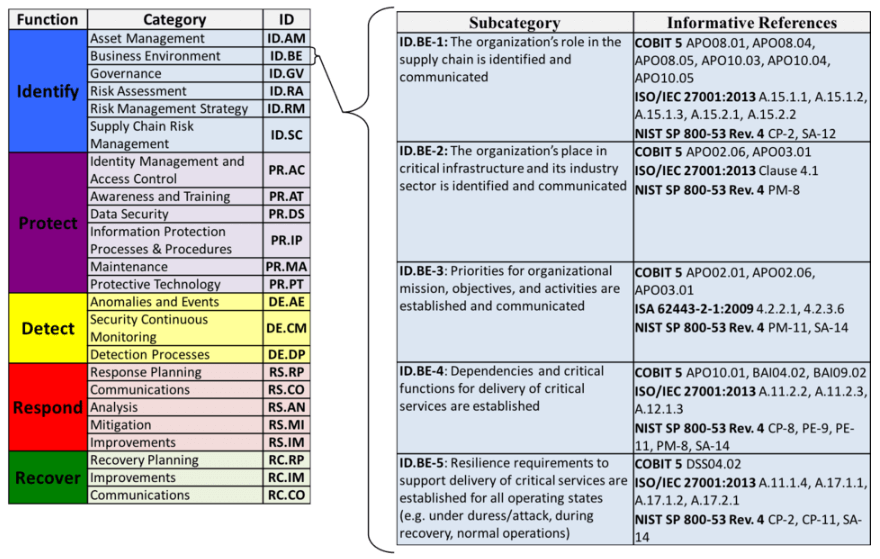
The Categories cover the breadth of cybersecurity objectives of an organization, while not being overly detailed. They cover topics across cyber, physical, and personnel. For example, access management and information protection. Each has a focus on business outcomes.
Subcategories are the deepest level of abstraction in the Core. There are 108 Subcategories. They are outcome-driven statements that provide considerations for creating or improving a cybersecurity program. In essence, these statements provide guidance on what to do to be more secure.
At this Subcategory level is where you “plug in” your current cybersecurity practices that are effective.
The image shows controls from COBIT or ISO/IEC 27001 that have been “plugged in” or applied. The Framework refers to those as Informative References.
Because the Framework is outcome driven and does not mandate how an organization must achieve those outcomes, it enables risk-based implementations that are customized to the needs of an organization.
Framework Implementation Tiers

Tiers describe the degree to which the cybersecurity risk management practices of an organization show the characteristics that are defined in the Framework. The Tiers range from Partial (Tier 1) to Adaptive (Tier 4). They describe:
- An increasing degree of rigor to be more secure
- How well you have integrated cybersecurity risk decisions into broader risk decisions such as organizational risk decisions, and
- The degree to which you share and receive cybersecurity information from external parties.
Tiers do not necessarily represent maturity levels. Organizations should determine a desired Tier.
- One that ensures that the selected Tier meets the goals of the organization
- A Tier that reduces cybersecurity risk to levels that are acceptable to the organization
- One that is feasible to implement
- And one that is financially justified
Framework Profiles
Profiles align the requirements, the objectives, the risk appetite, and the resources of your organization with the desired outcomes of the Framework Core.
Profiles can be used to identify opportunities for improving your cybersecurity posture by comparing a “Current” Profile with a “Target” Profile.
The identified gaps between the current state and the future target state serve as input for your improvement plan.
Why Use the Cybersecurity Framework?
The Framework provides a common language as well as a systematic methodology for managing cybersecurity risk. The Core includes activities you incorporate in a cybersecurity program. Those can be tailored to meet the needs of your organization. The Framework is designed to complement, not to replace, the cybersecurity program and the risk management processes of your organization. Check out these success stories on the NIST CSF website.
The process of creating Framework Profiles provides your organization with an opportunity to identify areas where existing processes may be strengthened. Or, where new processes can be implemented. These Profiles also allow for stronger communication throughout the organization.
Who Should Use the Framework?
The Cybersecurity Framework is for organizations of all sizes, all sectors, and all maturities.
While the Framework was designed with Critical Infrastructure (CI) in mind, think critical assets, it is extremely versatile.
The Framework has built-in customization mechanisms, The Tiers, the Profiles, and the Core, all can be modified. Therefore, the Framework can be customized for use by any type of organization. The Framework is outcome driven. And, it does not mandate how an organization must achieve those outcomes. It enables scalability. A small organization with a low cybersecurity budget, or a large corporation with a big budget, are each able to approach the outcome in a way that is feasible for them.
It is this flexibility that allows the Framework to be used by organizations which are just getting started in establishing a cybersecurity program, while also providing value to organizations with mature programs.
Call to Action!

Has this article sparked your interest? And would you like to learn more about NIST CSF? Then consider the following options.
- Have INTERPROM conduct a free NIST CSF Executive Brief and spread the word of improving your cybersecurity posture with NIST CSF
- Follow the links that are provided early in this article and download the PDF document of the NIST CSF framework. This document describes in great details how to use the framework.
- Participate in one of INTERPROM’s 1-day NIST CSF Foundation certification training courses.
- Conduct a self-assessment to raise awareness and/or identify gaps in the cybersecurity profiles. Or have INTERPROM conduct it for you.
- Allow us to coach your key players of the cybersecurity program or even your CISO and/or his or her direct reports during the journey of improving your cybersecurity posture
- Or, partake in our free cybersecurity self-assessment. Answer just 20 questions. And receive a 25-page custom cybersecurity improvement plan. Check it out!