
More and more Business Relationship Managers (BRMs) are being asked to help their organization with its information security challenges. This is not a surprise given the steady increase in malware attacks and other security breaches. While most BRMs are (temporarily) filling some the organization’s information security gaps, others are actively involved with raising security awareness. Few BRMs however, help navigating the organization on its journey towards establishing a robust information security management system.
This article explains the BRM’s role in help guiding the organization, so it is better and more proactively positioned to deal with the ever-increasing information security threats.
Information Security Management System

Let’s start with the basics of information security management. Information security is all about the preservation of confidentiality, integrity and availability of the organization’s information. Think of your customer list, your financial records, your sales records, your market research data, and your strategies for example. None of this should be for everyone to see.
The preservation of this information is best accomplished through establishing an information security management system, or ISMS. This system, ensures that whatever your organization needs to do in support of protecting its information is:
- Clear, concise and coherent
- Appropriate for the organization
- Well-understood by everyone in the organization
- Part of doing business-as-usual
- In-line with requirements and expectations of business partners
- In adherence with regulatory and contractual requirements
As a result, the ISMS, provides a set of information security best practices or capabilities for your organization to adopt.
Every ISMS is Unique

No two information security management systems are the same. While structurally they are the same, the execution of the activities and tasks involved, differ per organization.
Why is that, you may ask? While most organizations have similar information that needs to be preserved and protected, each will have unique information, that other organizations don’t have. For example, not every organization has patents that are to be protected. Or trademarks. Or homegrown software.
What is also unique per organization is the level of protection that is needed for its information. It differs depending on threat and vulnerability levels this information is exposed to. Or the risk appetite of the organization. Or the organization’s priorities regarding protecting its information. For example, does your facility have armed guards, a camera system, metal detectors, a key scan system and double entry doors? Or only one of the above? The risk level is certainly less in the first scenario.
Structure of the ISMS
The diagram below shows the common elements of every ISMS.
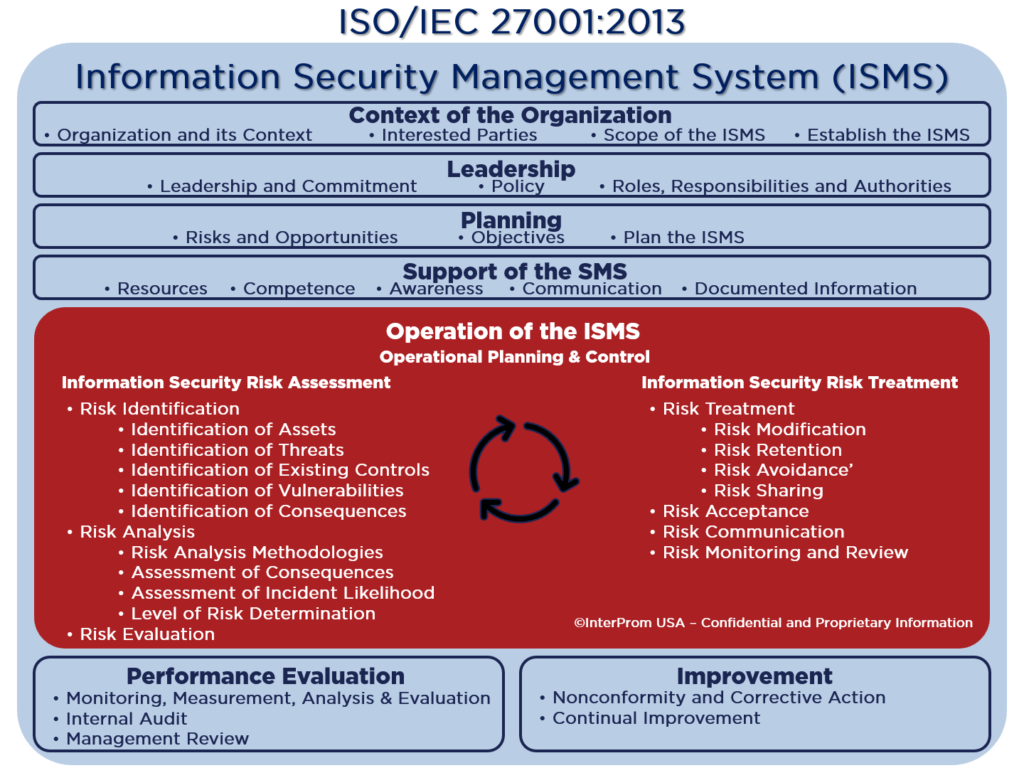
The capabilities in blue lay the groundwork for the capabilities in red. What that means is that the information security risk management capabilities (in red) are at the core of every ISMS. The other capabilities (in blue) facilitate these information security risk management capabilities. For example, leadership capabilities, communication capabilities, and measurement capabilities are in support of performing information security risk management.
Information Security Risk Management

Information security risk management is a capability during which the organization determines which information (assets) needs preservation of confidentiality, integrity and availability. It then determines the risks and risk levels this information is, or can be, exposed to. This is succeeded by determining what needs to be done to mitigate or treat these risks
The diagram below shows an elaborated version of how an ISMS works.

Establishing an ISMS
It takes four steps, or phases, to establish an ISMS:
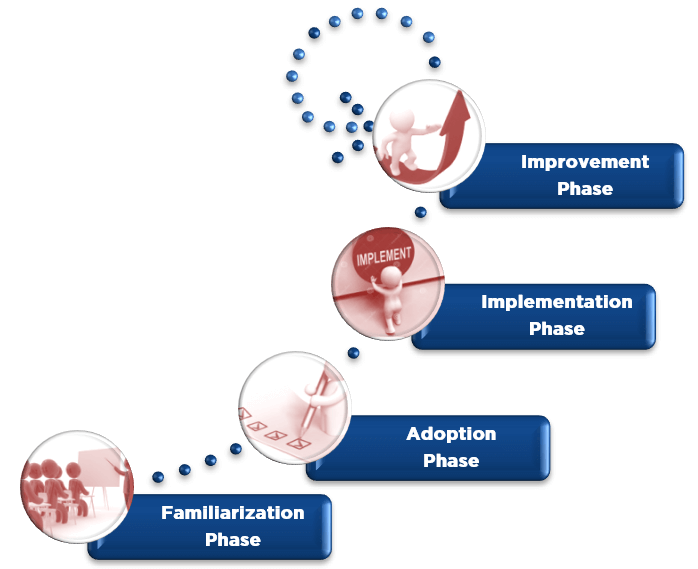
- Familiarize
- Adopt
- Implement
- Improve
Raising awareness in the organization around the concepts of information security, such as the information security management system and risk management is what the familiarization step is all about.
During the adoption phase the organization takes preparation steps such as assigning roles and responsibilities, conduct a gap analysis and agree on an implementation roadmap.
The implementation step is all about incorporating the capabilities of the ISMS into the organization’s existing capabilities or defining and implementing new capabilities. In other words, standing up the ISMS and making it part of business-as-usual.
The improvement phase is all about expanding the ISMS and increasing its robustness.
The BRM’s Role as an Explorer
First, I need to share with you that the words in bold font style in this paragraph and the following two all originate from the BRM Institute and are part of their intellectual property.
For organizations which lack the existence of a formal ISMS, the BRM could surface the need for it. And stimulate and orchestrate the conversation and discussion to establish one. Possibly supported through the BRM’s connections. Hint: Consider me one of your connections.
The BRM’s Role as the Navigator
Once the organization has embraced the idea of establishing an ISMS, the BRM’s role turns into being a navigator. You help the organization with staying the course during the four phases of establishing an ISMS or improving it.

This means that you stay informed about progress. You tap into your network of contacts when help is needed. You keep the initiative of establishing the ISMS focused on accomplishing its information security goals and objectives. Simply to ensure that the full value is harvested from it. Note: Use your business transition management skills to advise your organization while going through this organizational change.
The BRM’s Role and the Demand Shaper
Once the ISMS is established, it is time for the BRM to help extending and expanding its breadth and depth. Information security service levels (servicing) can always be sharpened. New risks may surface. And, risk levels will continuously change over time. And consequently, more or different risk treatments may have to be surfaced and implemented.

A successful ISMS positions the information security capabilities of the organization as a strategic asset. It enables the BRM to shape more or higher demands for this capability.
ISO/IEC 27001 and the BRM’s Toolkit
Every BRM should have a basic understanding of the international standard for information security management: ISO/IEC 27001. The standard is comprised of a checklist to establish an ISMS; an easy-to-use tool to raise awareness or to conduct a self-assessment with. It is supported by several other ISO standards. Particularly, ISO/IEC 27002 and ISO/IEC 27005. The former provides implementation guidance on risk treatment capabilities. The latter provides a structure for establishing information security risk management capabilities.
Call to Action for BRMs

- Download INTERPROM’s free white paper “What is ISO/IEC 27001?” and educate yourself a little more on what an ISMS is all about.
- Have INTERPROM conduct a free one-hour ISO/IEC 27001 Executive Brief and spread the word of the importance of robust ISMS per ISO/IEC 27001; a must-have in this information-security-day-and-age
- Purchase copies of the ISO/IEC 27001, ISO/IEC 27002 and ISO/IEC 27005 standards at iso.org or ansi.org and create your checklist to establish an ISMS
- Participate in one of INTERPROM’s ISO/IEC 27001 certification training courses. The exam is administered by APMG with whom most of you already have an account through your BRMP or CBRM exams.
- Conduct a self-assessment to raise awareness and/or identify gaps in the (non-)existing ISMS. Contact us for guidance on how you can do this relatively easy. Or have INTERPROM conduct it for you.
- Allow us to coach your key players of the ISMS such as your risk owners and your control owners. Or, even have us coach your Chief Information Security Officer (CISO) and/or his or her direct reports during the journey of standing up your ISMS
- Or, partake in our free cybersecurity self-assessment. Answer just 20 questions. And receive a 25-page custom cybersecurity improvement plan. Check it out!
Good luck with helping navigate your organization during its journey towards establishing a robust information security management system!
Important Links (in alphabetical order)
